intro
SSH tunnels are a well-known measure to securely forward connections to a remote machine. In most cases, SSH is fast, easy to setup, and easy to use, but it’s not without it’s drawbacks. Learn what they are in this blog.
Many developers know SSH tunnels inside out – many times they’re a prerequisite to working remotely, and sometimes they’re a necessity to complete work with websites, applications, or databases supporting them. Whatever the case, SSH tunneling is a method of working with data remotely via an SSH connection – and SSH is also commonly used as a method to create secure tunnels between different servers.
What Is an SSH Tunnel and SSH Tunneling?
In simple terms, a SSH tunnel is a method of working with data over SSH – short for a Secure Socket Shell (also sometimes called Secure Shell.) SSH is a way to securely access a server over an unsecured network.
Many companies use SSH, and the use case of SSH tunnels varies from company to company – some companies use SSH to access internal data to support their marketing, software engineering, security, or other efforts, some use SSH tunnels for interviews to grant people access to remote Amazon AWS servers for them to work with data to complete a task and provide a report on what they‘ve accomplished, some use them for other tasks.
However SSH tunnels are being used, their core premise remains the same – they provide people with a way to securely access their most precious data: a simple image would illustrate the concept of an SSH tunnel (8080, 22, and 80 are ports) – in this case, server #1 reaches the server #3 through server #2 (note that the port with which server #2 is accessed is no longer 8080 or 80 – it’s 22 meaning it has been accessed through SSH):

Security and SSH – the Downsides
As you might have understood, the core concept of SSH is the communication of two servers in an encrypted manner. In other words, the concept of SSH is secure communication, but SSH also has a couple of downsides that must be considered:
Reverse SSH Tunnel
Once you’ve considered all of the upsides and downsides posed by SSH, you might also be interested in functionalities related to SSH. One of such functionalities is the reverse SSH tunnel – a tunnel is frequently used to access an office PC from home, for example.
The concept of reverse SSH tunneling is establishing connections backwards – for example, from server B to server A instead of the other way around.
To create a reverse SSH tunnel, connect to a remote server using SSH like so:
$
ssh [username]@[serverip]
Then on the server B, run something like this:
$
ssh -fN -R 777:localhost:23 username@ipaddress
Where:
Once done, make an SSH connection request to the remote machine you want to access in a simple manner you’re used to, just make sure to specify the port like so (the port 777 will be forwarded to the port 23):
$
ssh username@localhost -p 777
You’re done!
Take note of the points mentioned above – before considering using SSH in any of your projects or at work, make sure to weigh each and every one of them very carefully, then decide if SSH is the option for you, and if it is, use it properly to avoid mishaps – this guide will guide you through most of the things you need to know, but the rest is up to you to figure out.
Summary
In this blog, we have walked you through the basic concept of SSH tunneling – we have walked you through what it is, how to work with it, and what problems can it cause to users when used improperly.
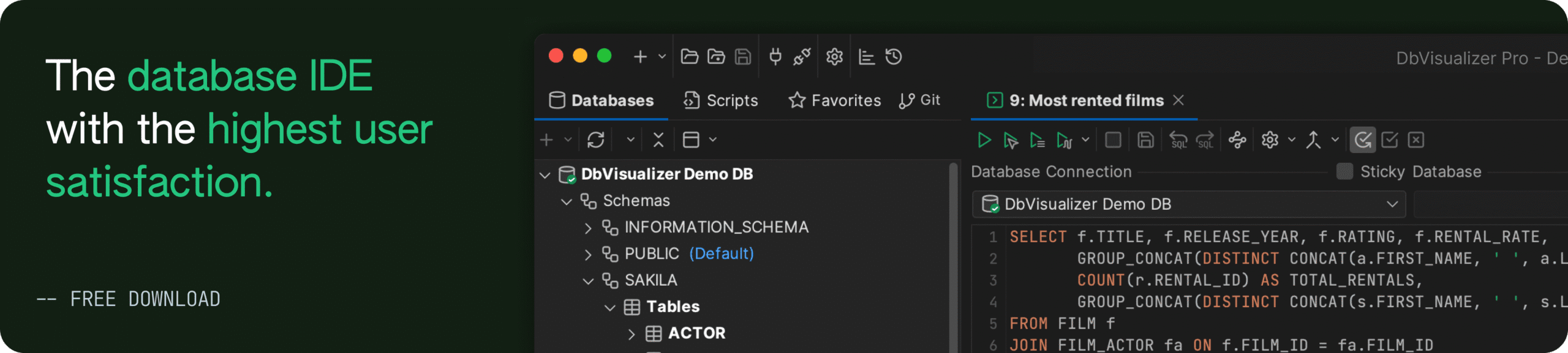
Take from this blog what you will, and make sure to test the advice you got from this blog before trying anything in a production environment. If you’ve enjoyed this article, make sure to stay around the DbVisualizer blog to learn more about databases, web development, and servers as well.