intro
There are many database clients available for you to use. In this blog, we’re walking you through the security side of them.
Welcome back! Previously, we’ve walked you through SQL interview questions, the comparison of different database clients in terms of diagrams and modeling, and covered a whole bunch of other things.
In this blog, we’re walking you through a set of database tooling again, just with a view towards security!
Database Clients and Security Considerations
First off, you should care about security no matter if you’re using an SQL client or not. Even if you decide that vanilla options like phpMyAdmin and the like are a better fit for your specific use case, you should keep in mind that data breaches do happen and while it’s true that hackers are often chasing around apps with the highest user count, that’s not always the case; your application may also become a target.
When choosing a database client, look into its features, evaluate them based on the features necessitated by your use case, and make an informed decision.
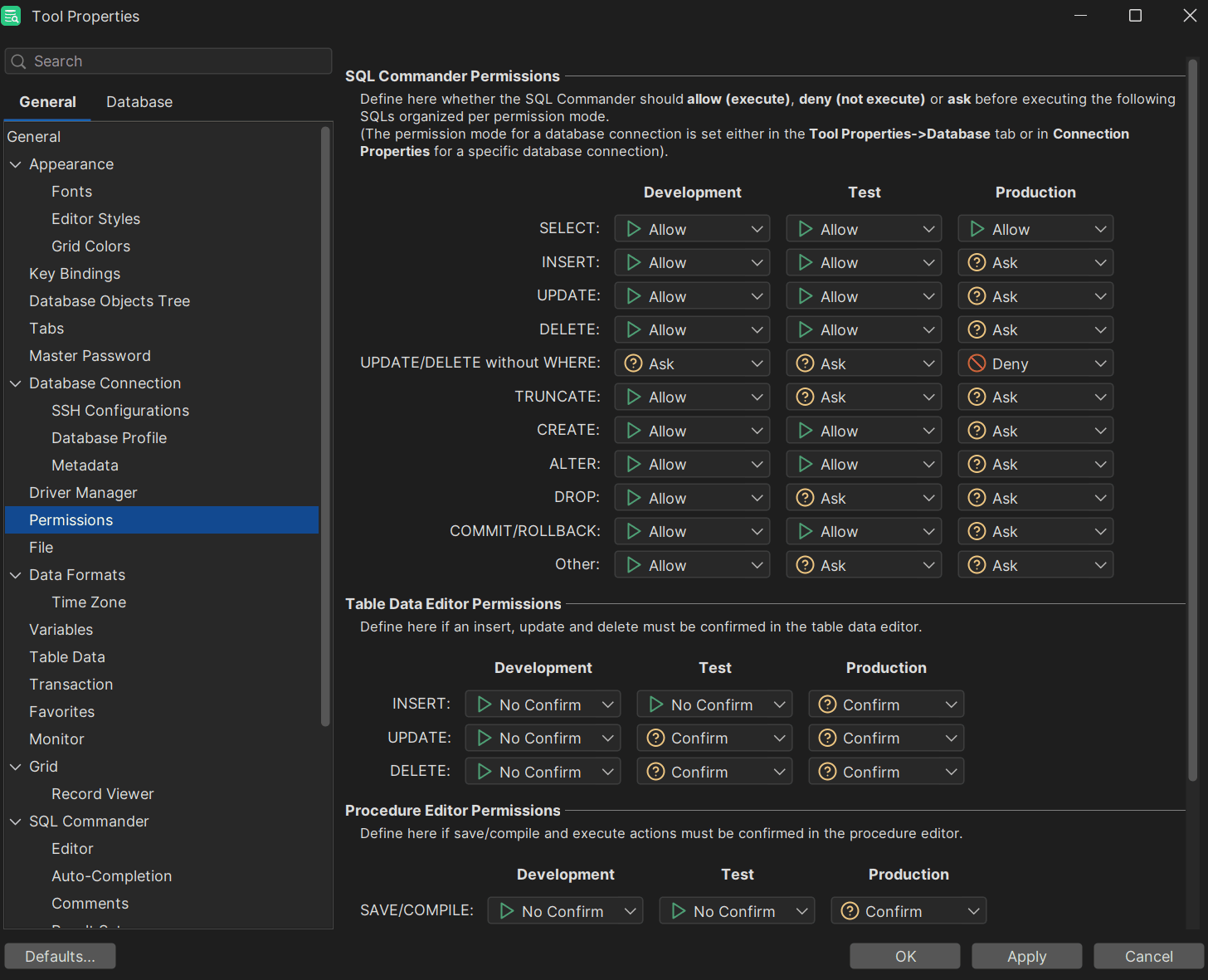
1. DbVisualizer: Comprehensive and Secure
What would this list of secure database clients be without DbVisualizer?
DbVisualizer is known to be a powerful and versatile tool with support for multiple database types, including MySQL, PostgreSQL, Redis, Elasticsearch, Snowflake, and more. It's known for its intuitive interface and the flexibility it offers for both novice and advanced users.
Security features include:
Besides this, DbVisualizer regularly runs penetration tests performed by third parties and while the results of those pentests may not be public, DbVisualizer can provide Letters of Attestation from a third-party provider upon request.
2. DBeaver: Open Source and Highly Secure
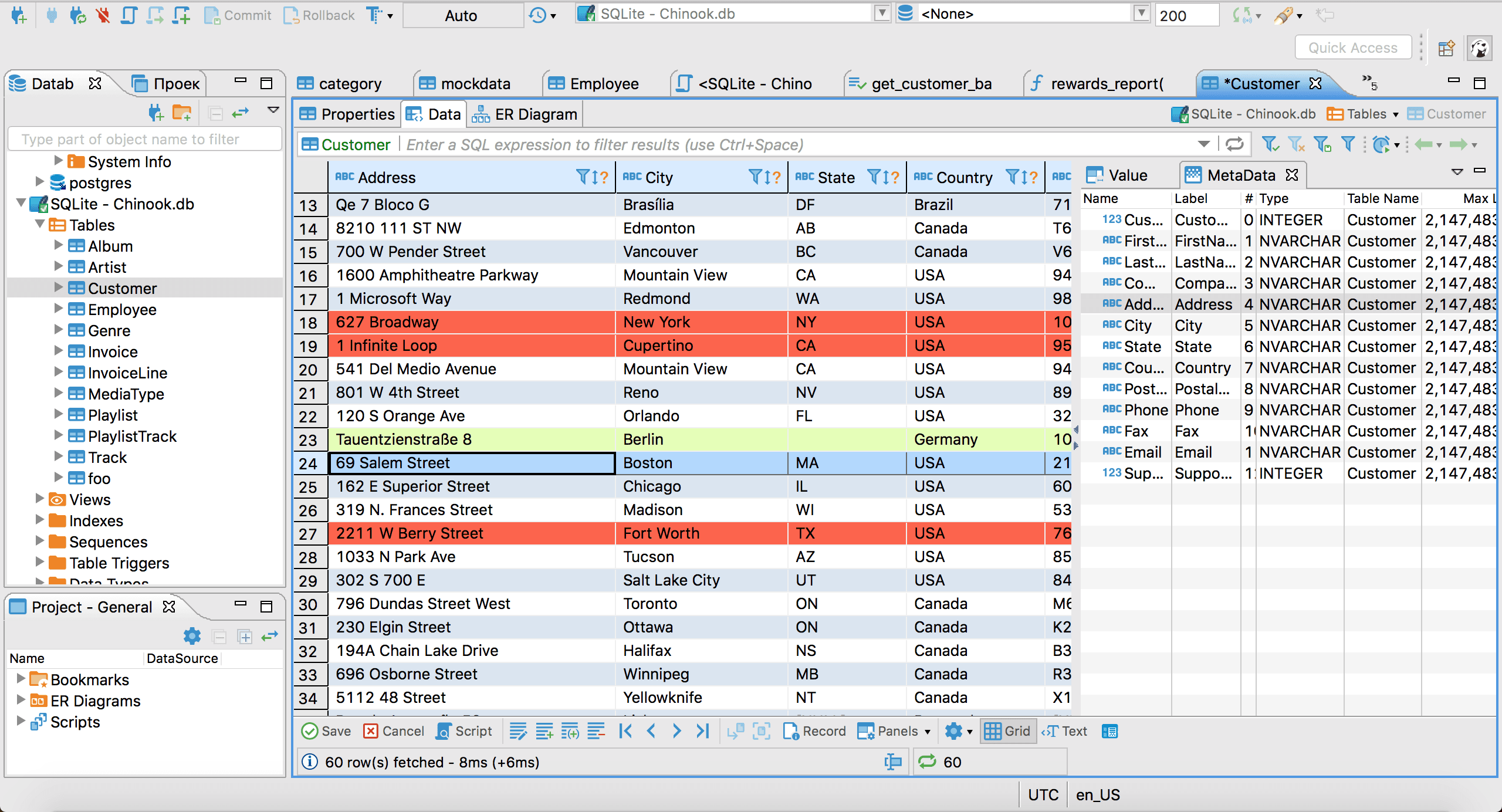
DBeaver is another widely used database management tool catering to a large community of developers, database administrators, and data analysts. DBeaver stands out for its open-source nature which makes it an attractive option for those seeking a flexible and a cost-effective solution.
Security features include:
3. HeidiSQL: A Lightweight Choice for DBAs
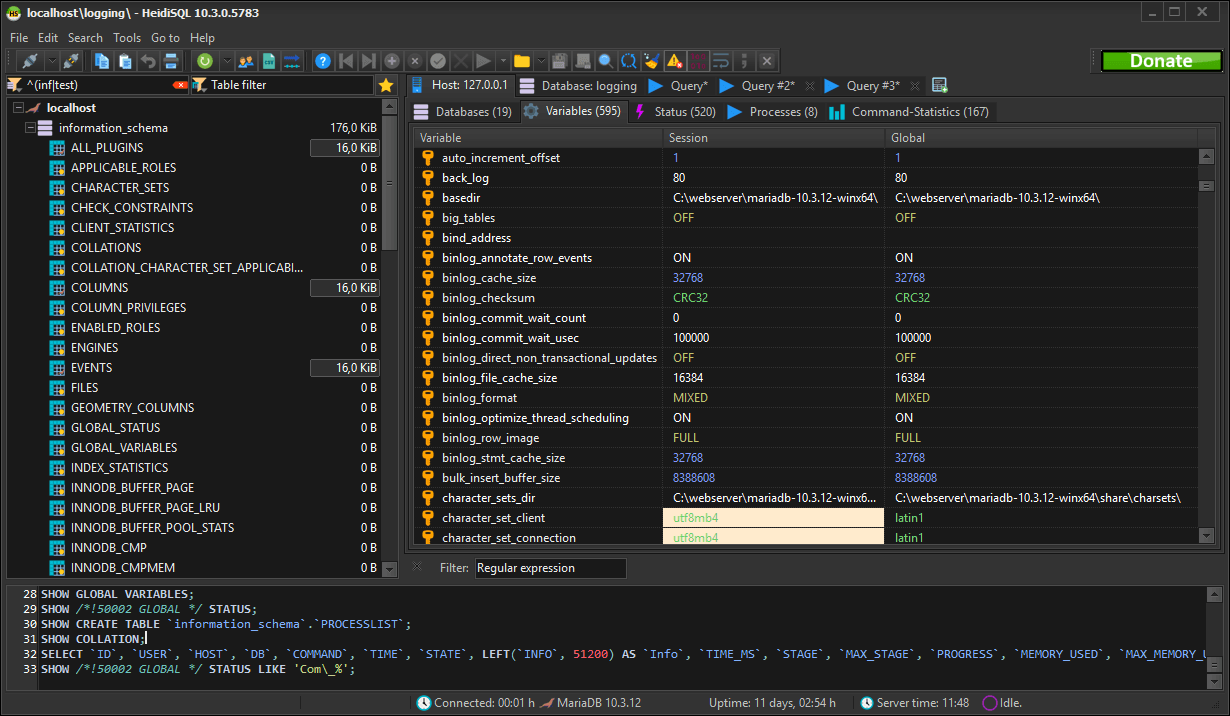
HeidiSQL is known to be a lightweight open-source database client that is primarily built around relational databases like MySQL and MariaDB, though it also supports other database management systems.
Security features include:
Being a lightweight choice, security features within HeidiSQL may be few and far between in comparison with other tools like DBeaver and DbVisualizer (it’s also made with Pascal, so it may look a little dated), however, if you’re only using MySQL and nothing else, perhaps it’s worth a shot.
Summary
In this blog, we’ve walked you through three different database clients from a security point of view. You have learned about the security capabilities of DbVisualizer, DBeaver, as well as HeidiSQL.
We hope that this blog has helped you see database clients from a different point of view and make an informed decision.
As always, though, do remember that security is only one part of managing data inside of your database: you also have to care about performance, high availability, and other things. To do that, follow blogs, read books pertaining to your specific DBMS of choice, and until next time.
FAQ
Which SQL database client is the most secure?
There’s no single database client that is “the most” or the least secure. Security features pertaining to SQL clients have to be weighed according to your specific use case and requirements, but at the same time, be advised that many security features within different database clients do intertwine so it’s likely that regardless of what database client you choose, you’ll be in good hands.
What should I do to secure my data and databases?
The things you should do to secure your database heavily depend on the database management system you find yourself using and your specific use case. However, reading up on the recent version of the OWASP Top 10 and staying aware of breach trends would always be a good start.